Autonomous
Threat Management
100% Autonomous AI Agents find, monitor, and reduce external threats. No manual work required.
No credit card required • Setup in 5 minutes • Cancel anytime
Trusted by Industry Leaders
150+ Enterprises Trust Hunto AI
From banking to fintech, e-commerce to healthcare: organizations worldwide rely on our autonomous threat protection.












What Hunto AI covers
One agent layer for external security work.
Your team gets coverage across exposure, people, brand risk, and operations without managing separate point tools for each job.
External exposure
Map domains, subdomains, cloud assets, exposed services, and forgotten systems before attackers use them.
Human risk
Run phishing simulations, measure risky clicks, and train employees based on their actual behavior.
Brand abuse
Detect phishing sites, fake social accounts, rogue apps, typosquats, and marketplace fraud.
Security operations
Triage alerts, investigate incidents, collect evidence, and escalate cases with context.
Security work your team stops chasing
Hunto AI handles high-volume security tasks across exposure, brand abuse, compliance, and response.
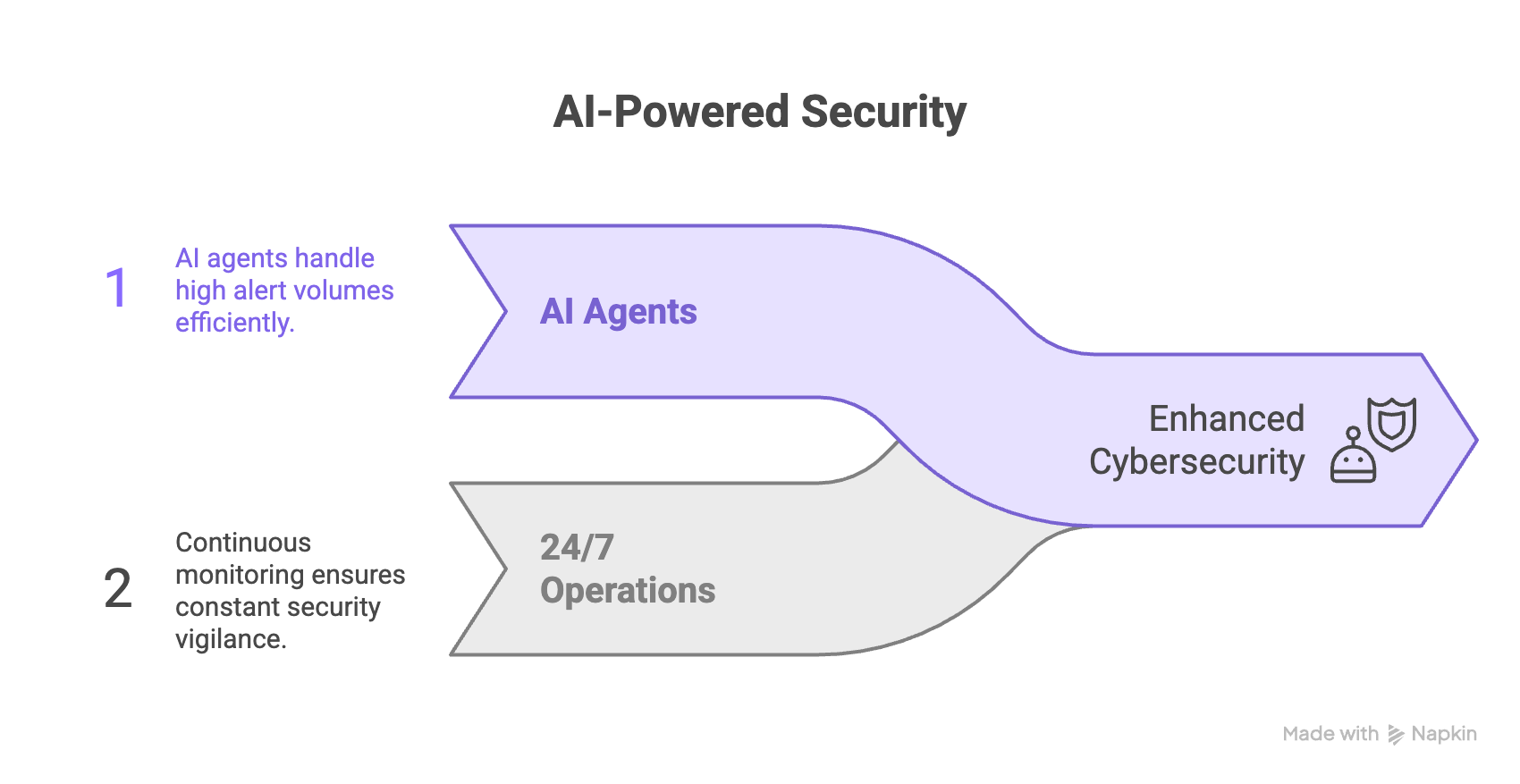
Continuous Threat Monitoring
Autonomous agents monitor public web, dark web, domains, cloud assets, and brand channels 24/7.
Early Signal Detection
Identify leaked credentials, exposed data, and attacker chatter before impact grows.
Threat Context
Attach evidence, severity, affected assets, and next steps to each finding.
Automated Takedowns
Detect phishing sites and impersonation, then send removal requests with evidence.
Audit-Ready Compliance
Collect evidence mapped to ISO 27001, SOC 2, GDPR, RBI, and other controls.
Unifies Your Stack
Connect alerts, tickets, chat, cloud, identity, and SIEM data in one workflow.
Connect tools fast,
start with live context.
Connect your security stack, map external assets, and start monitoring without a long deployment cycle.
- Asset and domain mapping
- Integrations with Slack, Jira, SIEMs, and cloud tools
- Historical scan and threat baseline
Evidence first,
clear action next.
Agents analyze headers, DOM structure, IP reputation, asset ownership, and historical signals. Your team gets confirmed findings with evidence.
- Forensic analysis of phishing kits
- Correlation with threat intelligence feeds
- Visual evidence and incident timelines
Global Impact
Security outcomes you can measure
Track asset coverage, takedown speed, compliance evidence, and threat response from the same platform.
Browse 15+ Success Stories
Real results speak louder than promises. Discover how enterprises across banking, fintech, and e-commerce achieved measurable security improvements with Hunto AI.
Read all case studiesA co-operative bank in Gujarat × Hunto AI
How a Gujarat co-operative bank strengthens digital trust with Hunto AI Industry Urban Co-operative Banking Scale Multi-branch retail and MSME bank […]
The Union Co-operative Bank × Hunto AI
How The Union Co-operative Bank protects its brand with Hunto AI Industry Urban Co-operative Banking Scale Multi-branch regional bank serving retail […]
Jodhpur Nagrik Sahakari Bank Ltd
How Jodhpur Nagrik Sahakari Bank protects its brand with Hunto AI Industry Urban Cooperative Banking Employees 200+ Product used Hunto AI […]
Knowledge Hub
Guides, Templates & Playbooks
Use practical resources for audits, SOC operations, incident response, and board reporting. Built for teams that need templates they can use now.
Explore all resources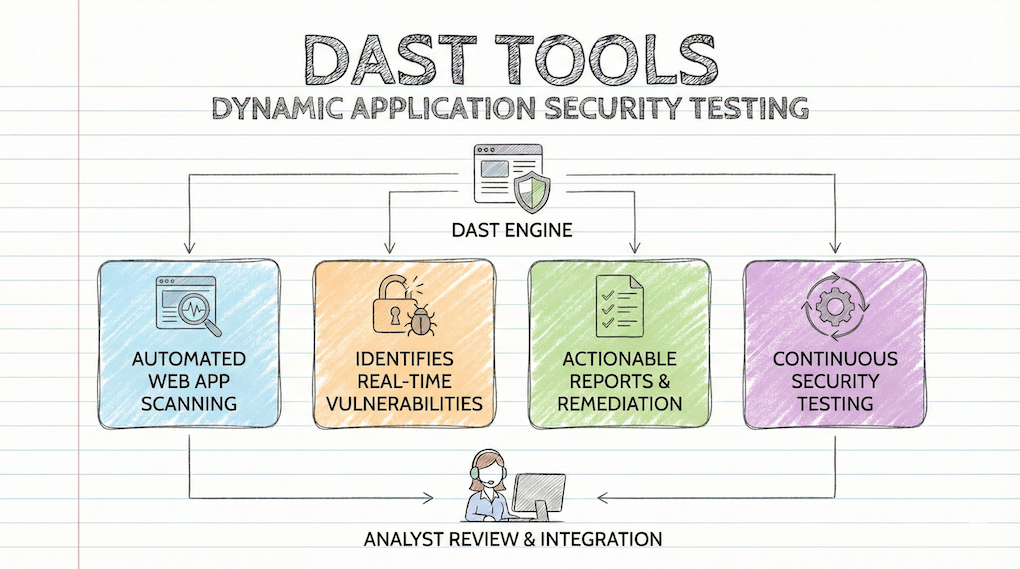
Top 10 Dynamic Application Security Testing Tools (2026)
Modern web applications are complex systems. They use multiple APIs, cloud services, and microservices to function. Securing these apps in 2026 […]
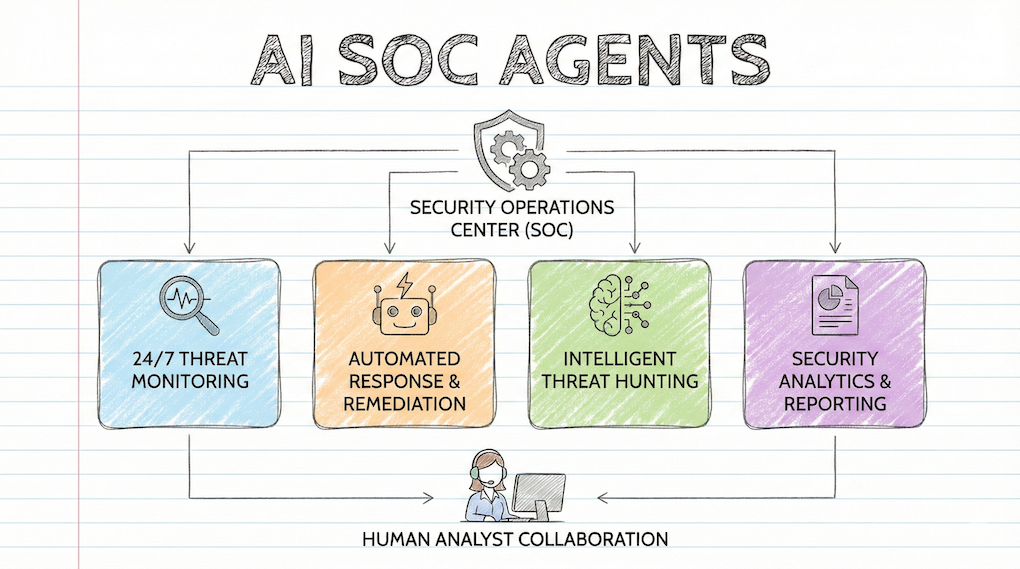
What Are AI SOC Agents? And How Do They Work – Detailed Guide
Modern Security Operations Centers (SOCs) are drowning in alerts and over burdened due to a shortage of skilled analysts. AI SOC […]
6 Best AI SOC Automation Tools for 2026
Security operations centers (SOCs) are drowning in alerts gloabally. Auto generated threats and alert fatigue are leaving cybersecurity teams overwhelmed. To [&
Frequently asked questions
Get clear answers about how Hunto AI protects your digital assets and brand from external threats.
Hunto AI runs external threat management with autonomous AI agents. It finds, monitors, and reduces threats across your digital footprint.
Legacy tools depend on manual triage. Hunto AI works 24/7, detects threats faster, responds with evidence, and keeps audit records ready.
Hunto AI protects against phishing, brand impersonation, domain spoofing, data leaks, credential theft, social media fraud, mobile app abuse, and external threats.
Yes. Hunto AI provides audit-ready evidence for RBI, ISO 27001, SOC 2, PCI DSS, HIPAA, GDPR, DPDP, and other frameworks.
Yes. Hunto AI connects to SIEM systems, email gateways, cloud platforms, and security tools through APIs.

Get A Free Demo
See how Hunto AI protects your digital presence with autonomous agents.