Attack Surface Management:
Autonomous Discovery, Monitoring & Protection
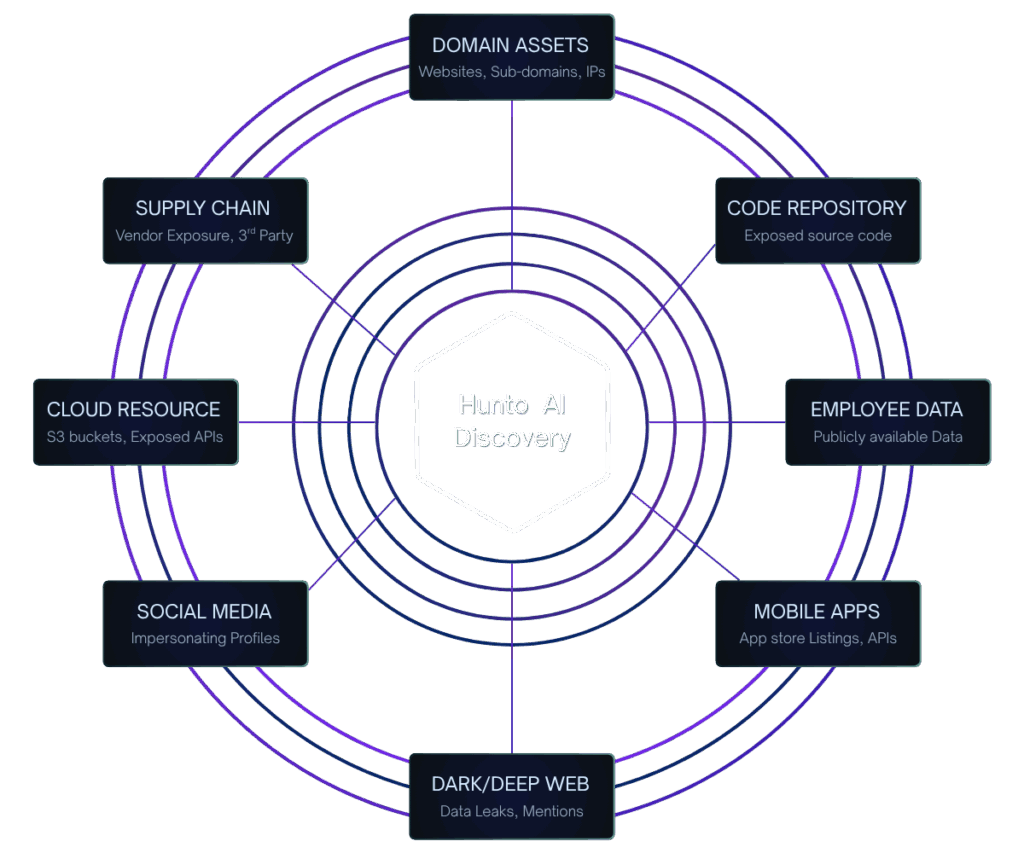
Complete external attack surface intelligence — from discovery to cloud ASM to remediation Continuous attack surface intelligence with AI-powered discovery, cloud attack surface management, vulnerability mapping, and real-time attack surface monitoring. Identify shadow IT, exposed services, and misconfigured assets before attackers do.
Hunto AI delivers next-generation cybersecurity from an attacker's perspective, ensuring complete External Threat Protection across all digital assets using Attack Surface Management. Our journey has been dedicated to setting the gold standard in threat counteraction, leveraging 90+ global partners and AI to perform 15,900+ successful takedowns last year. We are your strategic partner in eradicating threats and elevating security.
Solving External Attack Surface & Blind Spot Challenges
See how Hunto AI addresses your critical human-centric security needs.
Problem
Security teams lack comprehensive visibility into the rapidly expanding external attack surface, leaving Shadow IT, rogue domains, and unknown cloud assets exposed to sophisticated attackers
Solution
Hunto AI continuously identifies and inventories all external digital assets (cloud, mobile, on-premise) from an attacker's perspective, ensuring complete coverage and eliminating critical blind spots.
- Complete asset visibility, including Shadow IT.
- Continuous identification of all threats.
- Automated Drift Detection for instant alerting on system changes.
Key Capabilities of Hunto's Attack Surface Management
ASM provides the critical inventory of all external risk. Its continuous discovery and comprehensive vulnerability prioritization are seamlessly amplified by insights from Threat Intelligence and integrated with Digital Risk controls across the entire platform.
Continuous Intelligence-Driven Discovery
ASM's continuous mapping of the external attack surface is guided by real-time indicators of compromise (IOCs) and threat actor TTPs from our Threat Intelligence module. This ensures the discovery engine prioritizes scanning assets currently targeted in the wild.
Learn More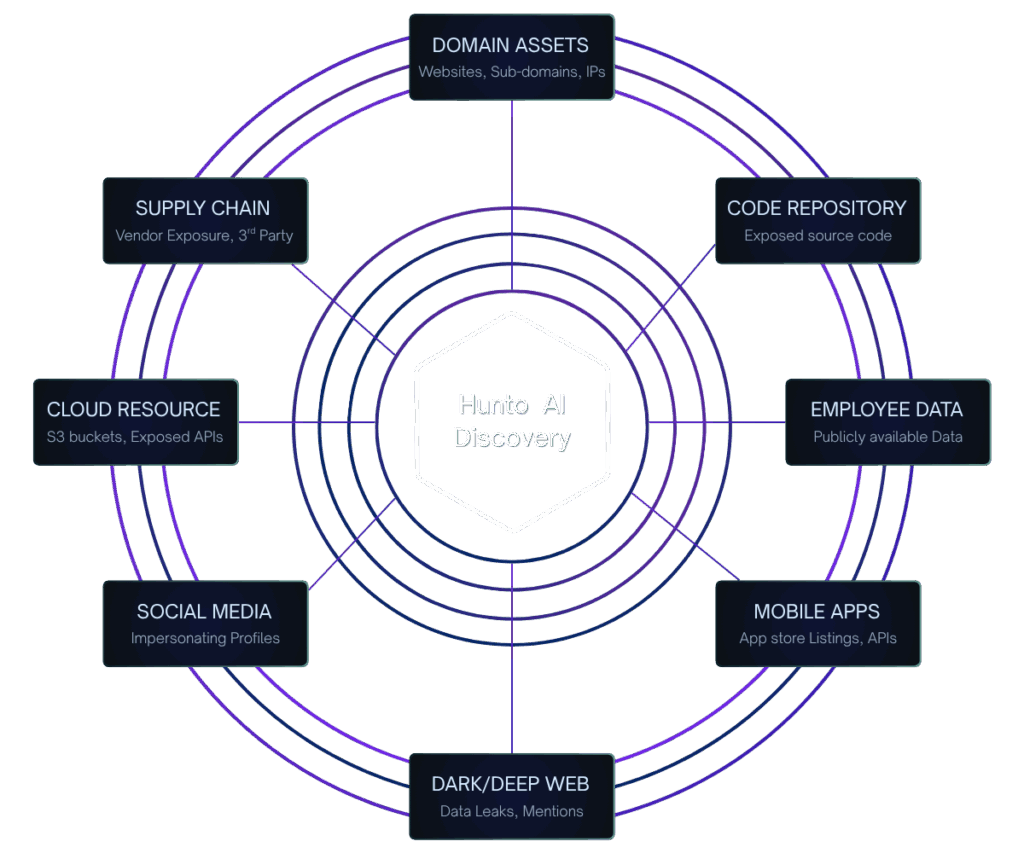
Validate External Risk Remediation
ASM validates the effectiveness of defensive measures by continuously checking known Digital Risk Protection (DRP) targets (e.g., fraudulent domains, fake social media). If a spoofing domain is missed by DRP, ASM identifies it as an unmitigated risk, closing the loop.
Learn More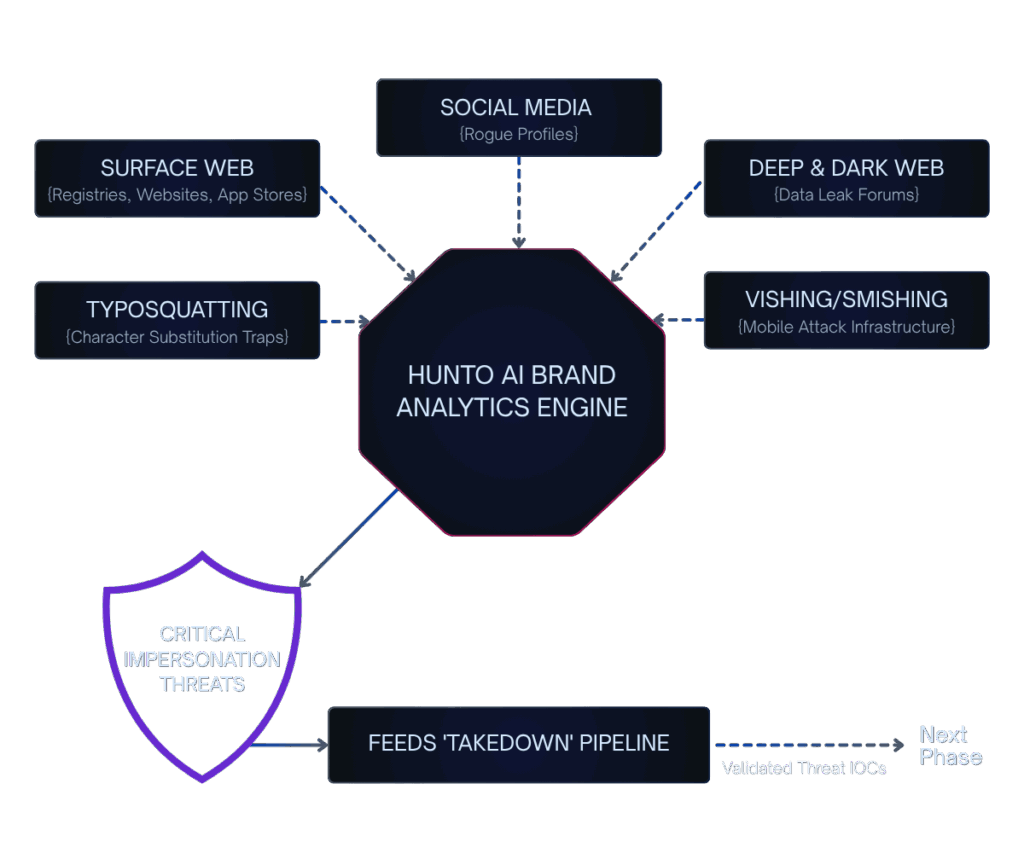
Vulnerability-Aware Human Risk Scoring
ASM's vulnerability prioritization identifies high-risk technical flaws (e.g., misconfigured email server settings, exposed RDP ports). This technical context is used to raise the Human Risk Number (HRN) of owners/teams responsible for those critical assets, driving accountability.
Learn More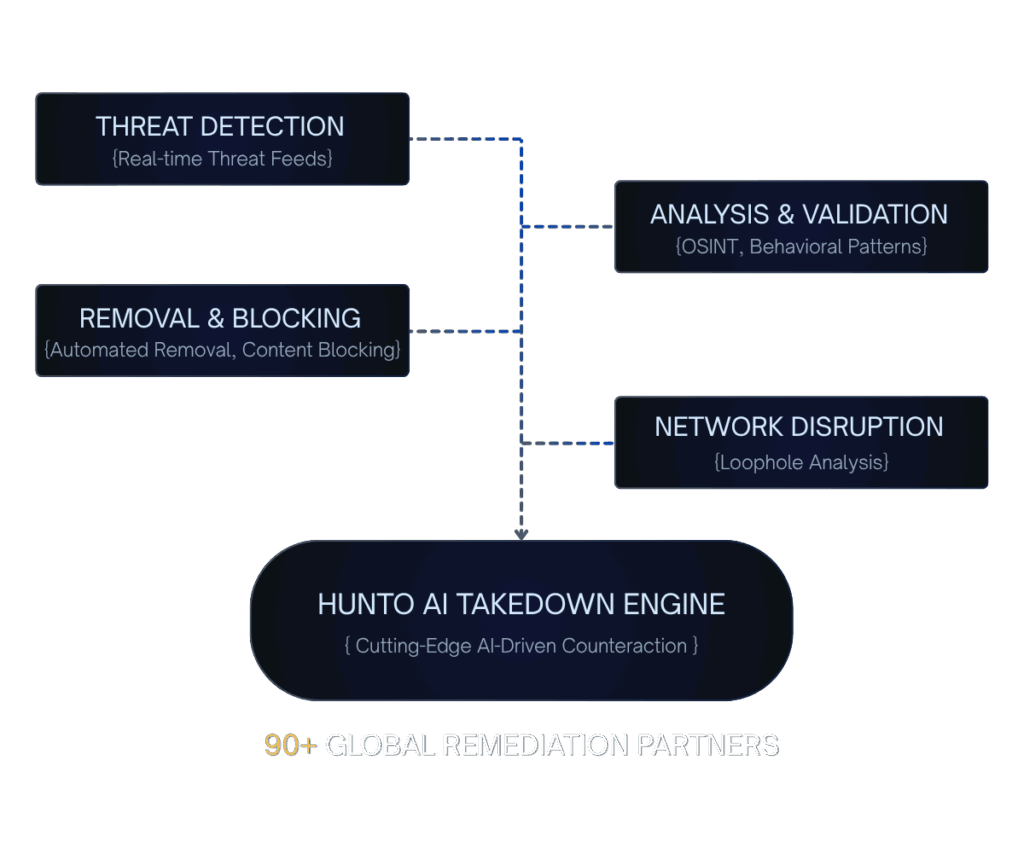
Measurable outcomes in just days.
Complete Asset Visibility
Discover 100% of your external attack surface including shadow IT, forgotten assets, and third-party exposures.
Real-Time Risk Prioritization
AI-powered scoring identifies critical vulnerabilities requiring immediate attention based on exploitability and business impact.
15,900+ Takedowns/Year
Automated threat neutralization removes fraudulent domains, phishing sites, and brand impersonation attempts.
Proactive Brand Risk Intelligence
Prevent attacks before they occur with predictive threat modeling and continuous external monitoring.
Automated Incident Response
Reduce response time from days to minutes with automated workflows and AI-assisted remediation.
Threat Intelligence Enrichment
Enrich vulnerability data with real-time threat intelligence to understand which assets are actively targeted.
What "Great" Looks Like (Built for Zero Trust)
See how Hunto AI secures your digital infrastructure against external threats and asset exposure.
Real-Time Attack Surface Discovery
Continuously identify all external digital assets, including Shadow IT, orphaned systems, exposed services, and forgotten domains across cloud, on-premise, and hybrid environments.
Attack Surface Intelligence Monitoring
Go beyond simple scanning with AI-powered attack surface intelligence that monitors, analyses, and prioritises threats based on real-time exploitation data and threat actor activity.
Multi-Vector Threat Remediation
Address 70+ types of cyber attacks including phishing, typosquatting, vishing, rogue apps, watering hole tactics, and exposed services — all from a single attack surface management platform.
AI-Powered Vulnerability Mapping
Attack surface intelligence mapping provides visual, contextual views of your external risk — showing which assets, services, and vulnerabilities pose the highest risk to your organisation.
Continuous Risk Prioritisation
Advanced algorithms assess vulnerability impact and exploitation likelihood, directing resources to the highest-risk exposures. AI-powered insights eliminate alert fatigue and focus your team.
Threat Intelligence Enrichment
Enrich attack surface intelligence with actionable insights from global threat feeds, IOC correlation, and attribution analysis derived from 1M+ data points analysed daily.
What Is Attack Surface Management?
Attack surface management (ASM) is the continuous process of discovering, inventorying, classifying, and monitoring all externally facing digital assets that an organisation exposes to the internet. Every domain, subdomain, IP address, cloud instance, API endpoint, and third-party integration represents a potential entry point for adversaries — and collectively they form your external attack surface. The goal of an attack surface management platform is to give security teams the same visibility that an attacker would have, then prioritise and remediate the riskiest exposures before they are exploited.
External attack surface management (EASM) specifically focuses on assets visible from outside the organisation's perimeter. This distinction matters because the modern enterprise perimeter has dissolved. Cloud sprawl introduces ephemeral infrastructure that spins up faster than IT can track. Shadow IT — services adopted by business units without security approval — creates blind spots that traditional vulnerability scanners never reach. Remote and hybrid workforces extend the attack surface to personal devices, home networks, and SaaS applications. Third-party integrations and supply chain dependencies further expand the set of assets that adversaries can probe.
Without continuous attack surface management, organisations operate with an incomplete and outdated understanding of their exposure. A forgotten staging server, an orphaned subdomain pointing to a decommissioned IP, or an exposed cloud storage bucket can each become the initial foothold for a breach. According to industry research, over 60% of breaches originate from previously unknown or unmanaged external assets.
Hunto AI addresses this challenge with autonomous, AI-driven attack surface discovery and monitoring. Our platform continuously maps your entire external footprint — including assets you didn't know existed — then applies real-time threat intelligence and risk scoring to focus your team on the vulnerabilities that matter most. Combined with digital risk protection capabilities, Hunto AI provides a complete view of external threats from asset exposure to brand abuse.
The Attack Surface Management Lifecycle
Effective attack surface management follows a continuous four-phase lifecycle. Hunto AI automates each phase with autonomous AI agents, eliminating the manual effort that causes coverage gaps and delayed response.
Attack Surface Discovery
The lifecycle begins with comprehensive asset discovery — identifying every internet-facing resource associated with your organisation. This includes known assets registered in your CMDB as well as unknown assets: shadow IT services, forgotten subdomains, orphaned cloud instances, development environments left exposed, and third-party integrations. Hunto AI's discovery engine analyses DNS records, SSL certificate transparency logs, WHOIS data, BGP routing tables, cloud provider APIs, and web crawl data to build a complete external asset inventory in real time.
Asset Inventory & Classification
Once discovered, each asset is catalogued with metadata: ownership, technology stack, hosting provider, geographic location, business function, and associated services. AI-powered classification automatically groups assets by type and criticality, distinguishing between production systems, staging environments, marketing microsites, and third-party dependencies. This structured inventory provides the foundation for risk-based decision making.
Risk Prioritisation & Vulnerability Analysis
Not all exposures carry equal risk. Hunto AI's AI engine scores each asset based on exploitability, active threat intelligence, business impact, and exposure level. A publicly accessible database with default credentials on a production server demands immediate attention; an informational disclosure on a marketing page does not. By correlating vulnerability data with real-world threat actor activity, the platform surfaces the exposures that attackers are most likely to target — not just the ones with the highest CVSS score.
Continuous Attack Surface Monitoring & Remediation
Attack surface monitoring is not a one-time scan — it must be continuous. New assets appear daily as cloud infrastructure scales, developers deploy services, and business units adopt new tools. Hunto AI monitors for configuration drift, newly exposed services, certificate expirations, and emerging vulnerabilities around the clock. When a critical change is detected, automated remediation workflows trigger — from notifying the asset owner to initiating an automated threat takedown for malicious infrastructure.
Attack Surface Management vs Vulnerability Management vs Penetration Testing
Security professionals frequently evaluate attack surface management alongside vulnerability management and penetration testing. While these disciplines complement each other, they serve different purposes and operate at different cadences. Understanding the distinction helps organisations build a layered security programme without redundant tooling.
| Aspect | ASM / EASM | Vulnerability Mgmt | Pen Testing |
|---|---|---|---|
| Scope | External-facing assets | Internal + external | Targeted systems |
| Frequency | Continuous | Periodic (weekly/monthly) | Point-in-time (annual/quarterly) |
| Automation | High — autonomous agents | Medium — scheduled scans | Low — manual expert-driven |
| Asset discovery | Yes — unknown assets found | No — scans known assets only | Limited — defined scope |
| Shadow IT detection | Core capability | — | — |
| Perspective | Attacker's view (outside-in) | Defender's view (inside-out) | Attacker simulation |
| Best for | External risk posture | Patch management | Compliance / deep testing |
Hunto AI delivers continuous attack surface management that complements your existing vulnerability management and penetration testing programmes. By maintaining real-time visibility into your external attack surface, the platform ensures that vulnerability scans and pen tests are scoped accurately — covering every asset, not just the ones your team already knows about.
What Does an EASM Tool Discover?
The value of EASM tools is measured by the breadth and accuracy of their discovery capabilities. A comprehensive external attack surface management platform must identify assets across every layer of your digital footprint — not just the domains listed in your DNS zone files. Hunto AI's discovery engine maps the following asset types automatically:
- ●Domains & subdomains — Primary domains, subdomains (including wildcard and dynamically generated records), and newly registered lookalike domains that could indicate phishing campaigns.
- ●IP addresses & CIDR ranges — IPv4 and IPv6 addresses, netblock allocations, and hosting provider associations for all internet-facing infrastructure.
- ●Cloud services & storage — AWS S3 buckets, Azure Blob containers, GCP storage, Lambda functions, and cloud-hosted databases that may be misconfigured or publicly accessible.
- ●APIs & web applications — REST and GraphQL endpoints, web application frameworks, and exposed admin panels or development interfaces.
- ●SSL/TLS certificates — Certificate transparency log analysis reveals subdomains and services, plus identifies expiring, weak, or misconfigured certificates.
- ●Open ports & exposed services — RDP, SSH, database ports, SMTP servers, and other services that should not be internet-facing.
- ●DNS & email infrastructure — MX records, SPF/DKIM/DMARC configurations, and email server exposure that could enable spoofing attacks.
- ●Code repositories & third-party services — Public GitHub/GitLab repos, leaked API keys, exposed configuration files, and third-party SaaS integrations linked to your organisation.
- ●IoT devices & forgotten assets — Internet-connected devices, legacy systems, orphaned infrastructure, and decommissioned services that remain accessible.
Hunto AI's easm tools go beyond simple asset enumeration by enriching each discovery with technology fingerprinting, vulnerability correlation, and ownership attribution — giving security teams the context they need to act immediately.
Top Attack Surface Management Use Cases
Attack surface management is foundational to multiple security and business initiatives. Enterprise case studies demonstrate how organisations leverage ASM across these critical scenarios.
Shadow IT Discovery & Governance
Business units routinely adopt SaaS tools, spin up cloud instances, and register domains without security team involvement. Shadow IT discovery is the most immediate value driver for attack surface management — revealing the assets your team doesn't know about but attackers can easily find. Continuous monitoring ensures new shadow IT is identified within hours of deployment, not months.
M&A Due Diligence & Attack Surface Assessment
During mergers and acquisitions, understanding the target company's external attack surface is critical for accurate risk valuation. EASM tools rapidly map the acquisition target's digital footprint — uncovering unknown assets, unpatched vulnerabilities, and compliance gaps that could represent inherited risk or hidden remediation costs.
Supply Chain & Third-Party Risk Assessment
Your attack surface extends to every vendor, partner, and service provider with access to your systems or data. External attack surface management enables continuous monitoring of third-party security posture — identifying exposed services, outdated software, and misconfigurations in your supply chain before they become your breach. AI agents for cybersecurity automate the continuous assessment that manual vendor questionnaires cannot achieve.
Compliance Auditing & Continuous Monitoring
Regulatory frameworks including PCI DSS, SOC 2, ISO 27001, and GDPR require organisations to maintain an accurate inventory of internet-facing assets and demonstrate continuous monitoring. Attack surface management provides the automated evidence collection, audit trails, and reporting that compliance teams need. Hunto AI's continuous compliance platform integrates ASM findings directly into GRC workflows.
Incident Response Preparation
When a breach occurs, the first question is always: "what assets are affected?" An up-to-date external asset inventory dramatically accelerates incident scoping and containment. Attack surface monitoring provides the asset context that incident responders need to determine blast radius, identify affected services, and prioritise recovery — reducing mean time to containment from days to hours.
Cloud Security Posture & Drift Detection
Cloud environments change constantly — new instances, modified security groups, exposed storage, and configuration drift happen daily. Continuous attack surface management detects these changes in real time, alerting security teams to publicly exposed databases, open management ports, and misconfigured access controls before attackers discover them. This is especially critical for multi-cloud environments where visibility gaps between AWS, Azure, and GCP create compounding risk.
Choosing an Attack Surface Management Platform
The EASM market has expanded rapidly, but not all platforms deliver equivalent value. When evaluating attack surface management vendors, focus on these criteria to ensure you select a solution that scales with your organisation and integrates into your existing security operations.
Discovery Speed & Completeness
How quickly does the platform discover new assets after they appear on the internet? Leading EASM tools detect new subdomains, cloud instances, and exposed services within hours — not days or weeks. Hunto AI's continuous discovery engine identifies changes in near real-time using multiple data sources simultaneously.
Asset Classification Accuracy
Raw asset lists without context create noise instead of clarity. Evaluate how accurately the platform classifies assets by type, technology stack, ownership, and business criticality. AI-powered classification should automatically distinguish production systems from staging environments and assign risk context without manual tagging.
Risk Prioritisation & Threat Intelligence
Vulnerability counts alone don't indicate real risk. The best attack surface management platforms correlate asset data with active threat intelligence — showing which exposures are being targeted by threat actors right now. This intelligence-driven prioritisation eliminates alert fatigue and focuses your team on genuinely critical issues.
Integration with Security Stack
An isolated ASM platform creates another silo. Verify integration with your SIEM, SOAR, ticketing systems, and vulnerability management tools via APIs, webhooks, and standard formats like STIX/TAXII. Hunto AI integrates with Splunk, Sentinel, Jira, ServiceNow, and other leading platforms to embed attack surface data into existing workflows.
Evidence Quality & Reporting
Strong evidence packages — asset screenshots, technology fingerprints, vulnerability details, network topology — support faster remediation and compliance reporting. Executive dashboards, trend analysis, and exportable audit trails should be standard, not premium add-ons.
Continuous vs Periodic Monitoring
Some platforms still rely on weekly or monthly scan cycles. In cloud-native environments where infrastructure changes hourly, only continuous attack surface monitoring provides accurate visibility. Ensure the platform you select offers true real-time monitoring — not repackaged periodic scanning.
Frequently asked questions
External attack surface management (EASM) is the continuous process of discovering, inventorying, and monitoring all internet-facing digital assets associated with an organisation — including assets the organisation may not know about. EASM tools scan for domains, subdomains, IP addresses, cloud services, APIs, exposed ports, and third-party integrations from an attacker's perspective. Unlike internal vulnerability management, EASM focuses exclusively on what's visible from outside the network perimeter, providing the same view an adversary would have when planning an attack.
Vulnerability scanning tests known, pre-defined assets for known vulnerabilities on a periodic schedule. Attack surface management starts by discovering all external assets — including shadow IT and unknown infrastructure — then continuously monitors them for changes, misconfigurations, and emerging risks. ASM operates continuously from an attacker's perspective, while vulnerability scanning operates periodically from a defender's perspective on a fixed asset list. The two are complementary: ASM ensures your vulnerability scanner covers your entire external footprint.
Hunto AI discovers domains, subdomains, IP addresses, CIDR ranges, cloud services (AWS, Azure, GCP), APIs, web applications, SSL/TLS certificates, open ports, exposed services (RDP, SSH, databases), DNS and email infrastructure, code repositories, third-party SaaS integrations, IoT devices, and orphaned or forgotten assets. Our discovery engine uses DNS analysis, certificate transparency logs, WHOIS data, BGP routing, cloud provider APIs, and web crawling to identify both known and unknown assets across your entire external footprint.
Hunto AI's continuous discovery engine detects new external assets within hours of their appearance on the internet. Unlike platforms that rely on weekly or monthly scan cycles, our AI agents monitor multiple data sources in real time — including DNS changes, certificate transparency logs, and cloud provider events. Automated drift detection triggers instant alerts when new assets appear, configurations change, or previously secure services become exposed.
Yes. Attack surface management directly supports compliance with PCI DSS (asset inventory and continuous monitoring requirements), SOC 2 (demonstrating security monitoring controls), ISO 27001 (information asset management), GDPR (identifying systems that process personal data), and other frameworks that require organisations to maintain accurate inventories of internet-facing systems. Hunto AI generates compliance-ready reports, audit trails, and evidence packages that map ASM findings to specific regulatory requirements.
Yes. Hunto AI integrates with leading SIEM and SOAR platforms including Splunk, Microsoft Sentinel, IBM QRadar, and Palo Alto XSOAR via REST APIs, webhooks, and STIX/TAXII. Attack surface discoveries, vulnerability findings, and drift alerts feed directly into your existing workflows and ticketing systems (Jira, ServiceNow). These integrations ensure that ASM data enriches your security operations rather than creating another isolated tool.
Explore more modules

Get A Free Demo
Ready to safeguard your organization's digital presence? Choose your plan and start your free trial.