Autonomous SOC:
Security Operations on Autopilot
Complete autonomous security operations — from alert to containment Hunto AI's autonomous SOC eliminates alert backlogs, investigates every threat in under 10 minutes, and responds to incidents without human intervention. Pre-built AI agents + custom agents for your environment — deploy in minutes, not months.
How Hunto AI's Autonomous SOC Works
See how AI agents transform security operations from reactive to autonomous.
Problem
Security teams struggle to integrate disparate tools and maintain comprehensive visibility across their entire security ecosystem.
Solution
Hunto AI connects to your SIEM, EDR, email security, cloud providers, identity systems, and ticketing tools via read-only APIs. No data migration, no vendor lock-in.
- Read-only API integrations
- No data migration required
- Multi-cloud and hybrid support
- Real-time data synchronization
Key Capabilities of Hunto's Autonomous SOC
AI agents handle the complete security operations lifecycle, from triage to containment, with human oversight for strategic decisions.
Zero-Playbook Investigation
AI agents reason dynamically through threats without rigid scripts that break on novel attacks. Unlike SOAR platforms requiring hundreds of playbooks, Hunto's agents adapt to new threat patterns automatically.
Learn More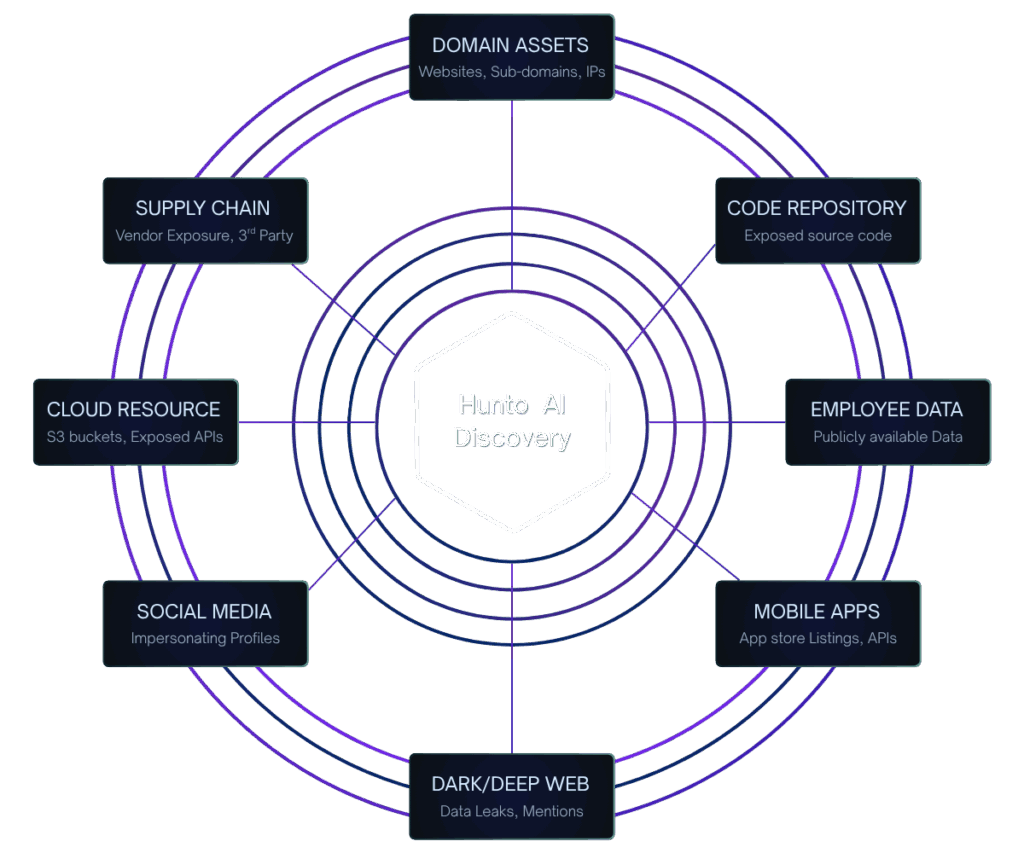
24/7/365 Coverage
Every alert is investigated immediately, every shift is fully covered. No backlog, no blind spots, no reliance on human availability. The autonomous SOC never sleeps, never takes breaks, never gets overwhelmed.
Learn More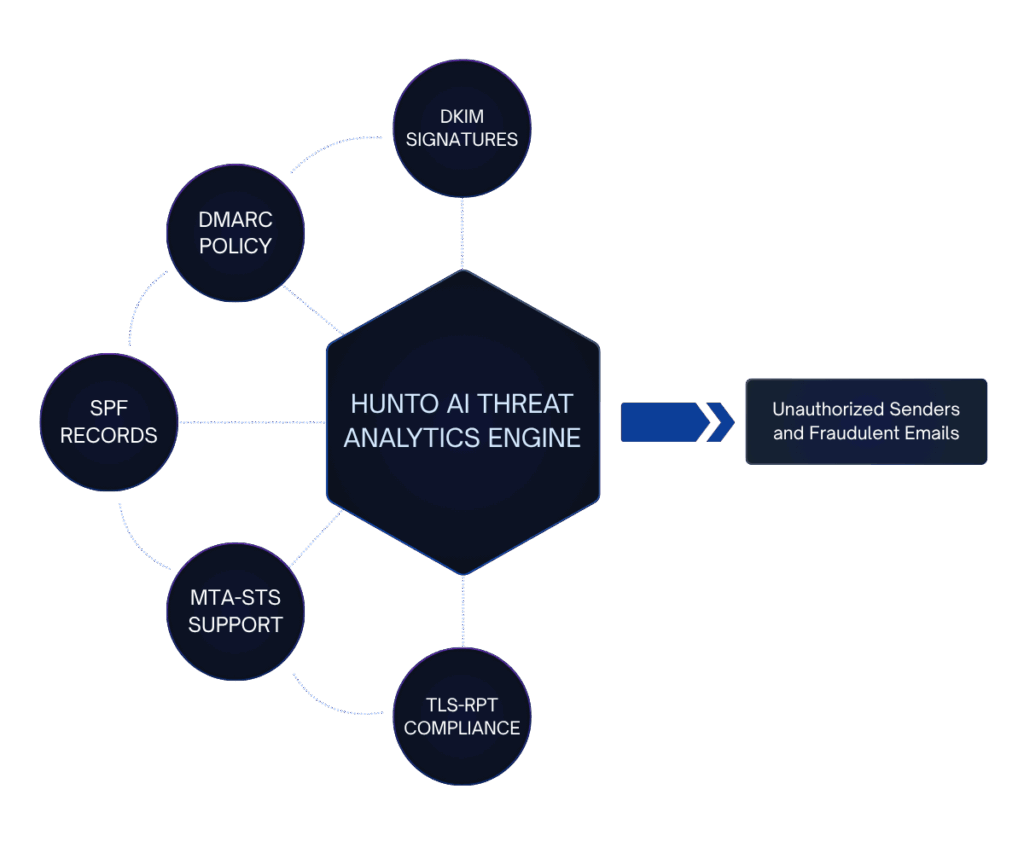
Sub-10-Minute MTTI
From alert to full investigation report in minutes, not hours. AI agents parallel-process evidence gathering across all tools simultaneously, achieving investigation speeds impossible for human analysts.
Learn More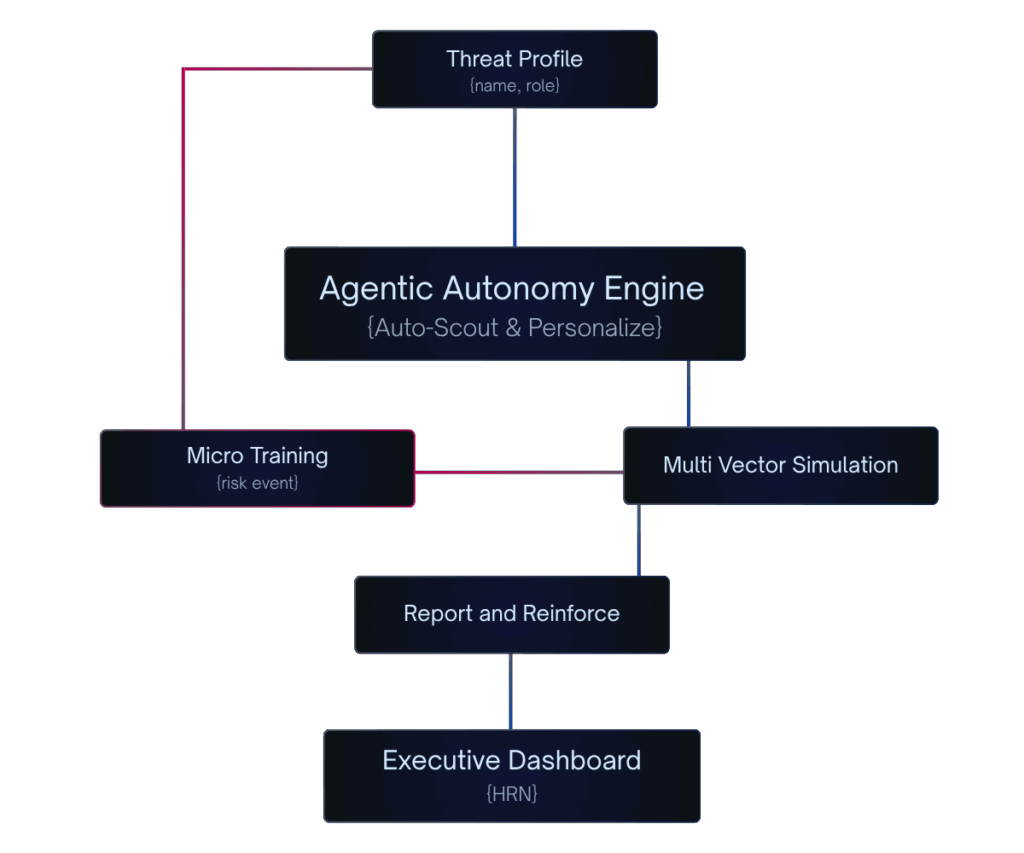
Multi-Agent Orchestration
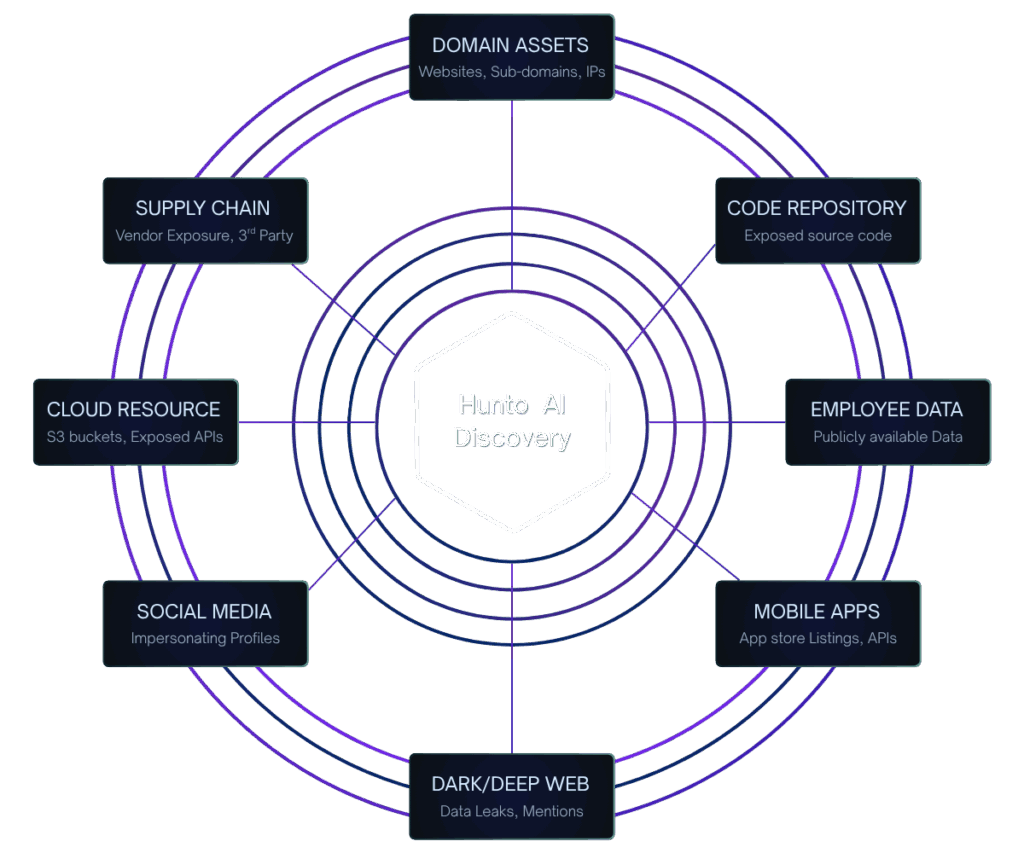
SOC agents collaborate seamlessly with ASM, dark web, phishing, brand protection, and GRC agents for cross-domain intelligence. Threats are investigated holistically across the entire attack surface.
Learn More
Custom Agent Deployment
Build and deploy AI agents specific to your organization's policies, tech stack, and compliance requirements. Your autonomous SOC adapts to your environment, not the other way around.
Learn More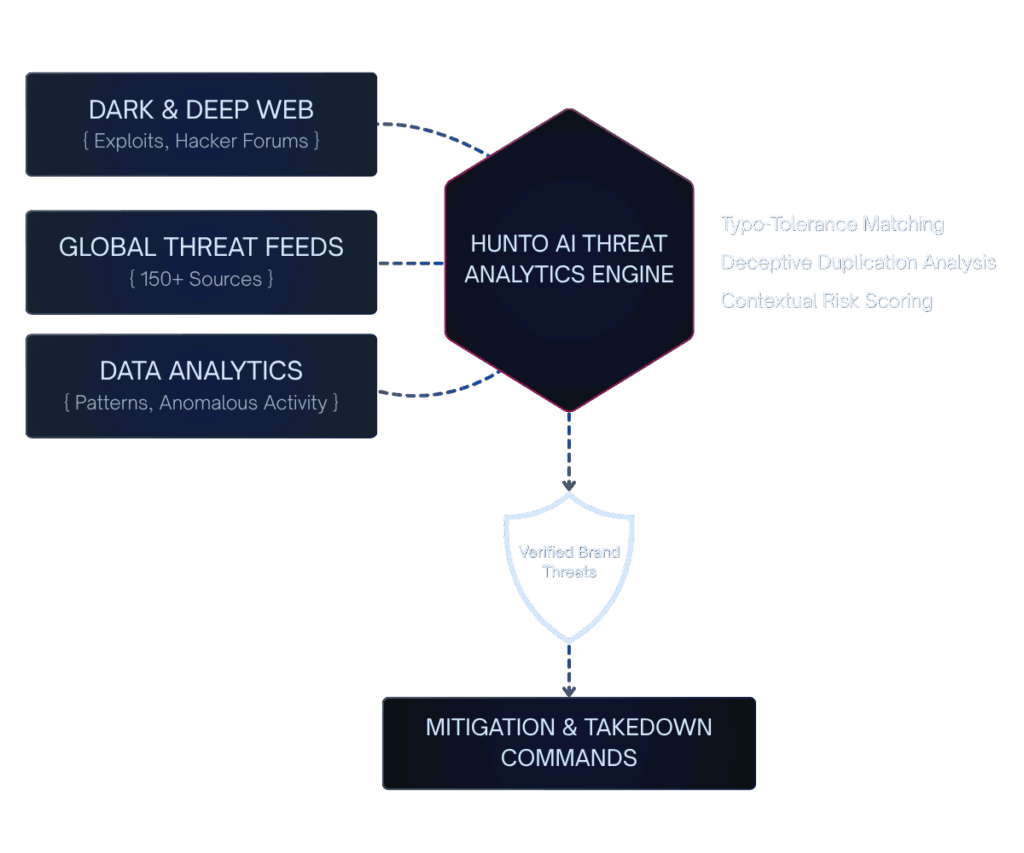
Human-in-the-Loop Controls
Set autonomy levels per agent type and maintain full transparency into reasoning and actions. Humans retain strategic oversight while AI handles the tactical execution.
Learn More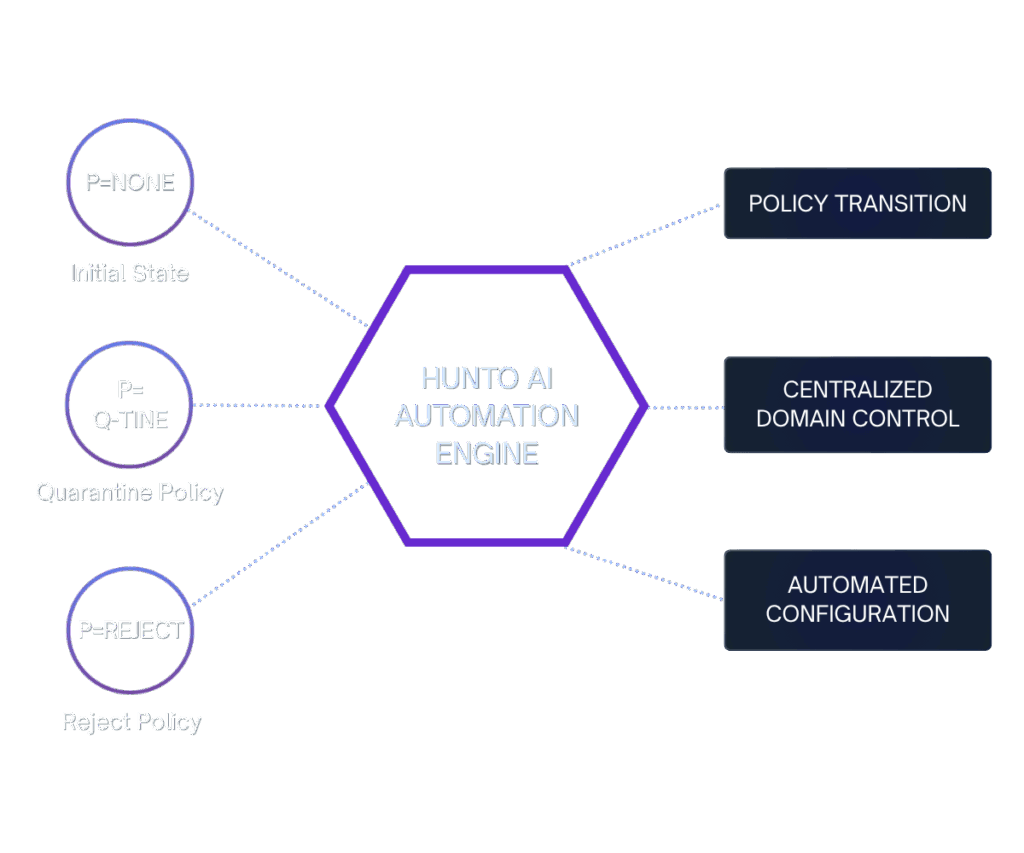
Measurable outcomes in just days.
100% Alert Investigation
Close the 99.5% investigation gap. Every alert gets full triage and investigation.
Minutes, Not Hours
Reduce investigation time from 25-40 minutes to sub-10 minutes per alert.
Zero Human Burnout
Eliminate alert fatigue and analyst burnout with AI handling routine operations.
Real-Time Response
Contain threats in real-time, not days. Reduce breach dwell time dramatically.
Scale Without Hiring
Handle 10x more alerts without adding headcount. Scale security operations infinitely.
Proactive Threat Hunting
Free analysts for strategic work. Shift from reactive firefighting to proactive hunting.
What "Great" Looks Like (Built for Zero Trust)
See how Hunto AI transforms traditional SOC operations into autonomous, AI-driven security.
Zero Alert Backlog
Every security alert is triaged and investigated immediately. No more 99.5% investigation gap — achieve 100% alert coverage with AI agents that never get overwhelmed.
Sub-10 Minute Investigations
Complete threat investigations in minutes instead of hours. AI agents gather evidence across all tools simultaneously, mapping blast radius and building comprehensive reports.
24/7 Autonomous Operations
Security operations run continuously without human intervention. AI agents handle routine triage, investigation, and response while humans focus on strategic threat hunting.
Dynamic Threat Reasoning
AI agents adapt to novel threats without rigid playbooks. Unlike traditional SOAR that breaks on unknown patterns, autonomous agents reason through any scenario.
Cross-Domain Intelligence
SOC agents collaborate with ASM, dark web, and brand protection agents for holistic threat context. No more siloed security tools working in isolation.
Audit-Ready Compliance
Every AI agent action is logged with full reasoning trails. Compliance becomes a byproduct of security operations, not a separate manual process.
What is an Autonomous SOC?
An autonomous SOC (Security Operations Center) uses AI agents to handle the majority of detection, investigation, and response tasks without requiring human intervention for routine operations. Unlike traditional SOCs where analysts manually triage every alert, or SOAR-based SOCs that rely on rigid playbooks, an autonomous SOC uses agentic AI that reasons through threats dynamically, investigates with contextual understanding, and takes containment actions in real-time.
Traditional SOCs are failing under the weight of alert volume. The average SOC receives 11,000+ alerts per day (Forrester), but analysts can realistically investigate fewer than 50. That's a 99.5% investigation gap. Meanwhile, attackers with AI move at machine speed. Human-dependent SOCs can't keep pace, leading to average breach identification and containment times of 258 days (IBM).
An autonomous SOC closes this gap with AI agents that never sleep, never burn out, and investigate every single alert. Humans set strategy, define guardrails, and handle escalated cases. Gartner predicts multiagent AI in threat detection and incident response will grow from 5% to 70% of AI implementations, primarily to augment staff overwhelmed by alert volumes.
Hunto AI's autonomous SOC goes beyond traditional definitions by integrating with the broader cybersecurity platform. SOC agents collaborate with attack surface management, dark web monitoring, phishing simulation, brand protection, and GRC agents for cross-domain intelligence that no isolated SOC tool can provide.
Why Traditional SOCs Are Failing
Four fundamental problems plague traditional SOC operations, creating massive security gaps that autonomous AI can solve.
Alert Fatigue & Investigation Gap
SOCs receive 11,000+ alerts daily, but analysts can only investigate ~50. That's a 99.5% gap where threats go undetected. Alert fatigue causes burnout, with 65% of SOC analysts reporting it as a major issue and average tenure dropping to 2 years.
Talent Crisis & Scaling Problems
There are 3.5M unfilled cybersecurity positions globally (ISC²). SOC teams can't scale to handle alert volumes, forcing organizations to choose between coverage gaps or unsustainable hiring costs.
Playbook Fragility
Legacy SOAR platforms require hundreds of playbooks, each taking weeks to build. They break when APIs change, cover only known attack patterns, and can't reason through novel threats. Most playbooks cover less than 1% of actual alert types.
Speed Gap vs AI-Powered Attackers
Attackers with AI move at machine speed. Human-dependent SOCs average 25-40 minutes per investigation and 258 days to contain breaches. This speed gap allows threats to spread undetected.
Hunto AI was built to solve all four problems simultaneously — with AI agents that never sleep, never burn out, and investigate every single alert. Traditional SOCs are reactive and overwhelmed; autonomous SOCs are proactive and comprehensive.
Autonomous SOC in Action
Real-world scenarios where Hunto AI's autonomous SOC transforms security operations.
Mid-Market Bank (BFSI)
A growing bank with a 4-person security team receives 5,000+ alerts daily from their SIEM and cloud infrastructure. Before Hunto: 95% of alerts went uninvestigated. With Hunto's autonomous SOC: every alert triaged in under 60 seconds, suspicious login attempts auto-investigated with full evidence chains, and RBI compliance evidence generated automatically. The team shifted from reactive firefighting to proactive threat hunting.
MSSP Scaling Operations
An MSSP managing 30 clients deploys Hunto's multi-tenant autonomous SOC. AI agents handle Tier 1 and Tier 2 triage across all clients, delivering 30-50% reduction in alert volume passed to human analysts. Custom agents per client encode org-specific escalation policies. Result: 4x more clients served without adding headcount.
SaaS Startup (Lean Team)
A 200-person SaaS company with zero dedicated SOC staff uses Hunto as their entire security operations function. AI agents monitor AWS, Google Workspace, GitHub, Okta, and Zendesk 24/7. Phishing simulation agents run monthly campaigns. GRC agents maintain SOC 2 compliance evidence continuously. Cost: a fraction of hiring even one SOC analyst.
Frequently asked questions
An autonomous SOC (Security Operations Center) uses AI agents to handle detection, investigation, and response to security threats without requiring human intervention for routine operations. Unlike traditional SOCs where analysts manually triage alerts, or SOAR-based SOCs that rely on rigid playbooks, an autonomous SOC uses agentic AI that reasons through threats dynamically, investigates with contextual understanding, and takes containment actions in real-time. Humans set strategy and handle escalated, complex cases.
Torq focuses on security hyperautomation — automating SOC workflows through integrations and playbook builders. Dropzone AI focuses specifically on Tier 1 alert triage. Hunto AI provides a broader autonomous platform: AI agents handle not just SOC operations but also attack surface management, dark web monitoring, phishing simulation, brand protection, and GRC compliance — all in one platform with custom agent deployment per organization.
No. An autonomous SOC augments human analysts by handling the high-volume, repetitive work (Tier 1 and Tier 2 alert triage, evidence gathering, routine containment). This frees human analysts to focus on strategic threat hunting, incident response for complex attacks, security architecture, and policy decisions. Think of it as shifting your team from reactive firefighters to proactive security strategists.
Hunto AI connects to your existing tools (SIEM, EDR, cloud, identity) via read-only APIs and begins investigating alerts immediately. Most deployments are operational within minutes, not weeks or months. Custom agents for organization-specific workflows can be deployed within days.
Yes. Hunto AI's autonomous SOC is built for regulated industries. It maps to compliance frameworks including RBI, SEBI, PCI-DSS, NYDFS, ISO 27001, SOC 2, NIST CSF, and HIPAA. Every AI agent action is logged with full reasoning trails, creating audit-ready evidence automatically. Compliance becomes a byproduct of your security operations, not a separate manual process.
Explore more modules

Deploy Your Autonomous SOC
Stop investigating 1% of your alerts. Start investigating 100%. Hunto AI's autonomous SOC deploys in minutes and starts working on Day 1.