12 Best Automated Phishing Simulation Tools [2026 Guide]
“Monthly Phishing Simulation” is no more effective as your human risk management strategy. In 2026, cybercriminals who perform phishing attacks do not operate on a schedule, and they certainly do not use static phishing templates. We have entered the age of Agentic Threats, where offensive AI agents scrape your employee data, craft hyper personalised lures, and execute campaigns at machine speed.
If your defence strategy relies on manual spreadsheets or legacy tools that require hours of admin work to launch a single campaign, you are already behind. The modern standard is Automated Phishing Simulation. These are “set and forget” platforms that use AI to continuously test, train, and inoculate your workforce against attacks that look and feel real because, in many cases, they are generated by the same AI models attackers use.
At Hunto, we are pioneering the shift to Agentic Security. We believe your defence should be as autonomous as the offence. While we offer the world’s first fully autonomous Phishing Simulation Agent, we believe in helping you find the right tool for your specific maturity level.
Table of Contents
What are Phishing Simulations?
Phishing simulations are a security practice where organizations send simulated malicious emails to their own employees to test their awareness and response to phishing attacks. The primary goal is to educate users and measure the effectiveness of security training, not to penalize them for mistakes. It’s a controlled exercise designed to build resilience.
Unlike a real phishing attack, which aims to steal credentials or deploy malware, a simulation is a safe training exercise. When an employee clicks a simulated link, they are met with a learning opportunity—such as an educational landing page—not a compromised machine.
How Phishing Simulations Work?
A modern phishing simulation follows a clear, automated lifecycle designed to test and train employees continuously. The process moves far beyond simply sending a fake email and seeing who clicks. It’s a closed-loop system of testing, data collection, and remediation.
The Phishing Simulation Lifecycle
Campaign Setup: It begins with defining the objective and scope. Are you testing the entire organization or a specific high-risk department like finance? The goal might be to reduce click rates, lower credential submission rates, or increase reporting rates.
Lure Creation: This is where modern tools diverge from legacy ones. Instead of picking from a static library of old templates, advanced platforms use AI to generate context-aware lures based on an employee’s role, department, and public information for maximum realism.
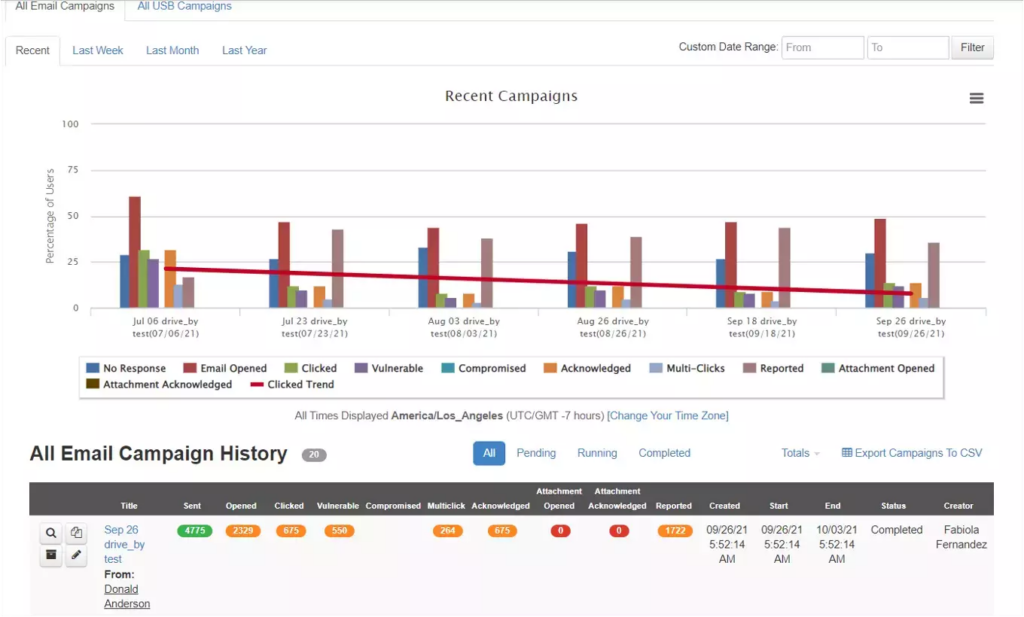
Execution: The platform then automates the delivery of these simulated phish. This isn’t a simple email blast; it can be staggered over days or weeks to mimic the unpredictable nature of real attacks and avoid office chatter that spoils the test.
User Interaction & Data Collection: When a user interacts with the email, the system tracks key metrics. Did they click the link? Did they enter credentials on the fake landing page? Or, ideally, did they use a reporting button to flag the email? We track click rates, compromise rates, and report times.
Remediation & Training: This is the crucial feedback loop. If a user clicks, they are immediately presented with ‘just-in-time’ training—a short video or a micro-learning module explaining the red flags they missed. Some platforms automatically enroll repeat-clickers into more intensive training courses.
Key Benefits of Phishing Simulations for Businesses:
Implementing these exercises offers several strategic advantages for reducing human risk and strengthening your overall security posture. The benefits are measurable and directly impact your ability to defend against real-world attacks.
Reduces Human Risk: The primary benefit is a quantifiable reduction in risky behavior. Based on our experience, organizations can reduce employee click-through rates by up to 90% within 12 months of implementing a continuous simulation and training program.
Strengthens Security Culture: Consistent simulations foster a proactive mindset. Employees transition from being potential victims to a human firewall, which we measure through a steady increase in phishing report rates—a key indicator of a healthy security culture.
Meets Compliance Mandates: Regular, documented phishing tests help satisfy security awareness training requirements under major frameworks. This includes PCI DSS for payment data, HIPAA for healthcare information, and ISO 27001 for information security management.
Provides Actionable Insights: Modern reporting tools pinpoint vulnerabilities with precision. You can identify high-risk individuals, see which departments are most susceptible (e.g., sales vs. engineering), and understand which attack types are most effective, allowing for targeted intervention.
What Makes a Phishing Simulation Automated or Agentic ?
Before listing the tools, it is critical to understand the shift from “Automated” to “Agentic.” The terms are not interchangeable; they represent different levels of sophistication and autonomy.
Legacy automation from the early 2020s meant you selected a template, uploaded a CSV of users, scheduled the blast, and looked at a static report. Today, agentic automation means the software acts as an autonomous operator, requiring virtually no human input after initial setup.
Manual vs. Automated vs. Agentic Simulation
Feature | Manual Simulation | Automated Simulation | Agentic Simulation |
|---|---|---|---|
Lure Creation | Manually selected from static library | AI-suggested from dynamic library | AI-generated, hyper-personalized lures |
Cadence | Scheduled, one-off campaigns | Scheduled, recurring campaigns | Continuous, behavior-triggered |
Admin Effort | High (hours per campaign) | Low (minutes per campaign) | Zero-touch (set and forget) |
An agentic platform moves beyond simple automation. It acts as an autonomous security analyst, making its own decisions. It discovers employee data, analyzes real-world threat intelligence, crafts unique lures for each user, and adapts its strategy based on their behavior—all without requiring a human operator to log in and configure campaigns. You need a tool that acts like a resident hacker, not a survey machine.
Top 12 Automated Phishing Simulation Tools
1. Phishing Simulation Agent by Hunto AI
Best For: Organizations seeking fully autonomous, “zero touch” human risk management.
Hunto is not just a simulation tool; it is an Agentic Cybersecurity Platform. Its phishing simulation agent is designed to completely remove the administrative burden from the security team while delivering the most realistic email phishing simulations on the market.
This agentic approach represents a fundamental shift from traditional, campaign-based simulations. Instead of periodic tests, Hunto provides a persistent, adaptive defense layer that trains employees continuously.
How It Works
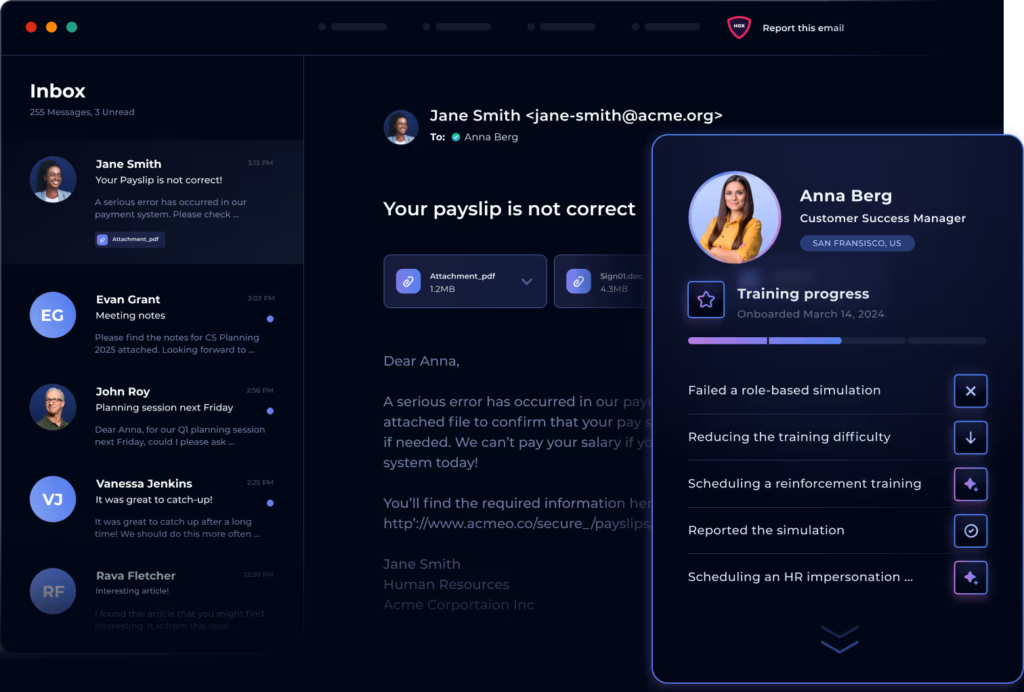
The core of the platform is the AI agent. Think of it as an automated red teamer assigned to each employee. The agent performs open-source intelligence (OSINT) gathering to understand the company’s public footprint and each user’s specific role and context. It then crafts and delivers hyper-realistic phishing emails one by one, learning from every interaction.
If a user reports a simulation, the agent learns what they can spot. If they click, the agent provides immediate, contextual micro-training and adjusts future simulations to reinforce the lesson. This creates a personalized, continuous training cycle that adapts to individual progress without any manual intervention from the security team.
Key Features
Autonomous Lure Generation: The AI agent scans your organization’s public news, social media, and tech stack to generate context-aware phishing lures. No templates. Just bespoke attacks that mimic real-world threats.
Continuous Simulation: Hunto abandons the campaign model for a persistent, low-and-slow approach. It sends simulations continuously, ensuring security awareness is always on, not just a quarterly event.
Real-Time Feedback: When a user fails a simulation, they receive instant, point-of-failure training. This immediate correction is proven to be more effective than delayed, generic training modules.
Slack & Teams Integration: Feedback and micro-trainings are delivered directly within the user’s workflow via Slack or Microsoft Teams, increasing engagement and minimizing disruption.
In our experience, this method drives rapid improvement. For example, a 500-employee tech firm using Hunto’s agentic approach reduced credential submissions in phishing tests by 85% within the first three months.
Pricing
Hunto’s pricing is transparent and value-based. Plans start at $48 per user per year for the Phishing Simulation Agent. For comprehensive human risk management including dark web monitoring and brand protection, contact the sales team for enterprise pricing on the full Autopilot platform.
2. Hoxhunt
Best For: Driving behavioral change through gamification and positive reinforcement.
Hoxhunt is a human risk management platform that excels at making security training an engaging, positive experience for employees. Instead of just testing and punishing failure, it gamifies the process of threat reporting, encouraging users to become active participants in the organization’s defense. Its AI-enabled engine delivers personalized micro-training moments that feel native to the user’s workflow.
The platform’s core strength is its focus on culture. By rewarding users with points and leaderboard status for successfully identifying and reporting both real and simulated threats, it creates a powerful positive feedback loop. The adaptive learning engine analyzes user skill levels, ensuring simulations are challenging but not frustrating. With strong support for multi-language deployments, Hoxhunt is a popular choice for global enterprises looking to build a security-conscious culture from the ground up. A key consideration is its lighter touch—teams wanting aggressive, red-team-style testing might find it too gentle.
3. Phished.io
Best For: Automated, hands off content generation.
Phished.io was one of the early adopters of AI driven content. Their platform emphasises “zero manual intervention.” The AI analyses threat trends daily to create new templates that mirror active campaigns in the wild.
Why it works:
Smart Scheduling: It determines the optimal time to send an email to a specific user to maximise the chance of engagement.
Checklist Free: There are no complex wizards to follow; the AI handles the campaign strategy based on the risk profile you define.
4. KnowBe4 (HRM+)
Best For: Content variety and compliance heavy industries.
As the market share leader, KnowBe4 offers the deepest library of training content in the industry. Their evolved HRM+ platform attempts to bridge the gap between their legacy training modules and modern behavioural data.
Why it works:
Massive Library: Thousands of templates and training videos, including high production value series that keep users entertained.
SmartGroups: Allows for granular targeting of user groups based on behaviour, location, or role.
Brand Recognition: A safe choice for auditors and compliance officers who look for established names.
5. Proofpoint Security Awareness
Best For: Threat intelligence driven simulations.
Proofpoint leverages its dominance in the email gateway market (SEG) to fuel its simulations. Because they see a vast amount of the world’s email traffic, they can turn real attacks blocked by their gateway into simulations instantly.
Why it works:
VAP (Very Attacked People): Identifies and targets training toward the specific individuals in your company who are being targeted by real attackers.
Attack Spotlight: Turns trending global threats into training modules in near real time.
6. Cofense (formerly PhishMe)
Best For: Integrating simulations with the SOC.
Cofense focuses on “conditioning” rather than just training. Their unique value proposition is the integration between simulation and the Security Operations Center (SOC). They view employees as human sensors who can report active threats.
Why it works:
PDC (Phishing Defense Center): Validates user reported emails to separate real threats from simulations.
Incident Response: Feeds reported phishing simulations directly into the incident response workflow, training the SOC team alongside the general staff.
7. Ironscales
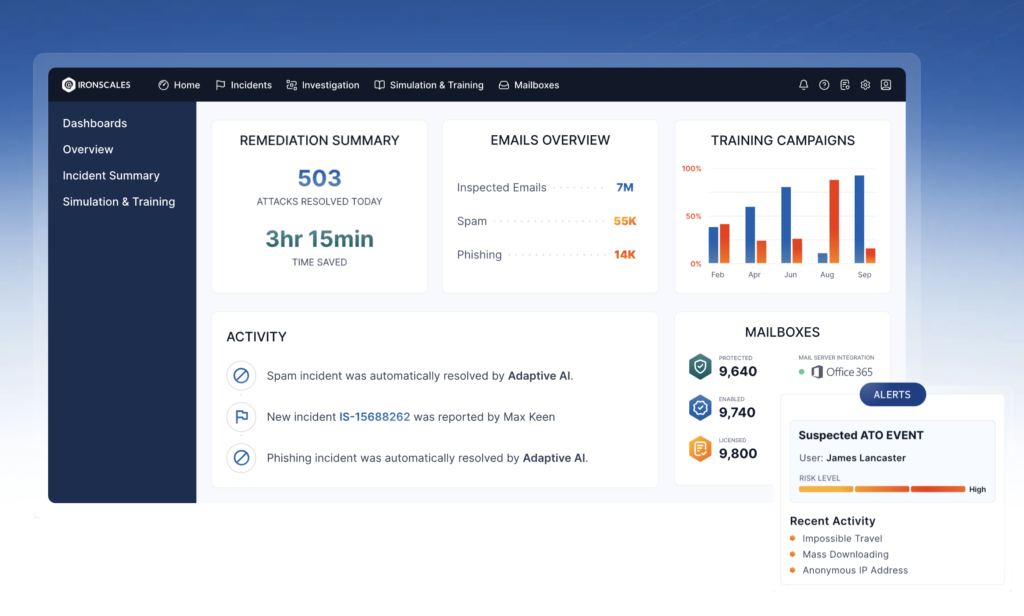
Best For: Integrated email security and simulation.
Ironscales combines protection and training in a single platform. It uses AI to detect anomalies in the inbox and uses that same intelligence to craft simulations.
Why it works:
Themis Co Pilot: An AI assistant that helps classify threats and suggests simulation scenarios.
Seamless Feedback: Users report phishing directly inside Outlook/Gmail, and the platform instantly analyses the message.
8. Arctic Wolf Managed Security Awareness
Best For: Organizations that want to outsource the entire process.
Arctic Wolf offers a “Concierge Security” model. Instead of giving you a tool, they give you a service. Their team manages the campaigns, analyses the data, and provides the reports.
Why it works:
Microlearning: Focuses on short, digestible content sessions (often <3 minutes) to maintain attention.
Zero Admin: Ideal for lean IT teams that do not have the bandwidth to manage a simulation tool.
9. Mimecast Engage
Best For: High quality, humorous training content.
Mimecast (formerly Ataata) is famous for realising that boring training gets ignored. Their content uses humour and “sitcom style” videos to engage users, aiming to reduce the “eye roll” factor of security training.
Why it works:
Watchability: Content that employees actually discuss at the water cooler.
CyberGraph: Graphs the relationship between users and external senders to customise risk scores.
10. Sophos Phish Threat
Best For: Existing Sophos Central users.
If you are already in the Sophos ecosystem for firewalls or endpoint protection, Phish Threat is a logical addition. It is managed from the same “Sophos Central” dashboard, allowing for consolidated reporting.
Why it works:
Unified Console: Manage endpoint, network, and email security training in one tab.
Synchronised Security: Can correlate a user’s simulation failure with their endpoint health status.
11. Infosec IQ
Best For: Deep customisation and role based education.
Infosec IQ offers robust features for organisations that want to tailor training to specific roles (e.g., developers vs. HR). It provides granular control over the simulation templates and the educational landing pages.
Why it works:
Workforce Scoring: Measures the “security culture” of the organisation, not just click rates.
Need to Know: Delivers specialised modules for compliance standards like HIPAA, PCI DSS, and GDPR.
12. PhishGrid
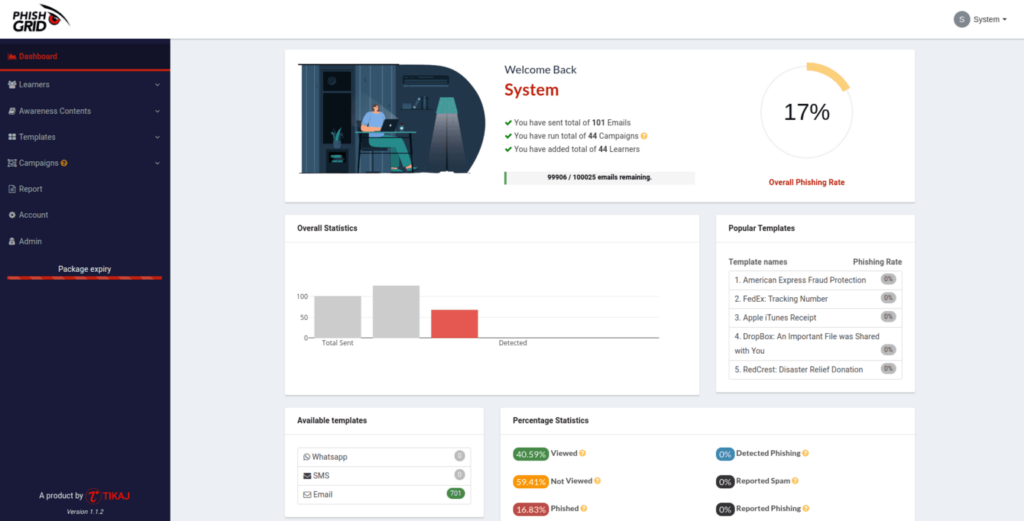
Best For: Flexible, API driven simulation and learning.
PhishGrid focuses on the intersection of simulation and interactive learning. It is designed to analyse an environment’s maturity and offers a more modular approach to training, often utilised by service providers.
Why it works:
Real Time Simulation: Emphasises the immediacy of feedback loops during the simulation process.
Comprehensive Reporting: Provides detailed analytics that allow teams to drill down into specific departmental vulnerabilities.
Comparison of Top Features:
Tool | Best For | Automation Level | Supports Vishing? | Supports Smishing? | AI-Powered Lures? | Automatic Remediation? | Pricing Model |
|---|---|---|---|---|---|---|---|
Hunto AI | Autonomous Operations | Agentic | Yes | Yes | Yes (Generative) | Yes (Instant) | Per User/Year |
Hoxhunt | Gamification & Culture | Automated | No | No | Yes (Adaptive) | Yes (Instant) | Per User/Year |
KnowBe4 | Content & Compliance | Manual/Automated | Yes | Yes | No (Templates) | Yes (Scheduled) | Tiered/Per User |
Proofpoint SAT | Threat Intel Integration | Automated | Yes | Yes | No (Threat-based) | Yes (Scheduled) | Per User/Bundle |
Cofense | Enterprise Threat Response | Automated | Yes | Yes | No (Threat-based) | Yes (Scheduled) | Per User |
IRONSCALES | Integrated Email Security | Automated | No | No | Yes (Adaptive) | Yes (Instant) | Per Mailbox/Year |
Mimecast | Email Security Suite | Automated | No | No | No (Templates) | Yes (Scheduled) | Per User/Bundle |
Phished.io | AI-driven Training | Automated | No | Yes | Yes (Generative) | Yes (Instant) | Per User/Year |
Tessian | Inbound Threat Defense | Agentic (Defense) | No | No | Yes (Behavioral AI) | Yes (In-the-moment) | Per User/Year |
GoPhish | DIY & Pen Testers | Manual | No | No | No | No | Open-Source (Free) |
Infosec IQ | Extensive Content Library | Manual/Automated | Yes | Yes | No (Templates) | Yes (Scheduled) | Per User/Year |
Sophos Phish Threat | Endpoint Integration | Automated | No | No | No (Templates) | Yes (Scheduled) | Per User/Bundle |
Why “Template Based” Phishing is Dead?
In the past, running a phishing simulation meant selecting a “Reset Password” template from a library and sending it to everyone. In 2026, this is ineffective for two reasons:
Polymorphism: Real attackers use AI to change the wording, subject, and sender of every email. A static template does not prepare users for this variety.
Context: A generic “Package Delivery” email is easy to spot. An email referencing a specific LinkedIn post you made yesterday about a conference in Vegas is terrifyingly effective.
Tools like Hunto.ai and Phished.io use OSINT (Open Source Intelligence) to gather public data and craft lures that act like real spear phishing. This “Red Teaming as a Service” approach is the only way to measure actual risk.
FAQs:
Do I really need AI for phishing simulations?
Yes, using AI for phishing simulations is essential in 2026 to keep pace with AI-driven attacks. Attackers now use generative AI to write flawless, context-aware emails at a massive scale, making old, template-based phishing attempts obsolete. Your defense must use the same advanced methods as your adversary.
AI-powered simulation tools create more believable, personalized, and varied phishing lures that mimic real attackers. They can reference a user’s department, recent company news, or professional connections to build credibility. This contrasts sharply with static, easily recognizable templates that train employees to spot only the most obvious fakes, leaving them unprepared for sophisticated, modern threats.
How often should I run phishing simulations?
The most effective phishing simulation frequency is continuous. We’ve found that running simulations in a constant, low-volume ‘drip’ is far superior to predictable monthly or quarterly campaigns that everyone comes to expect.
Mass-send campaigns create a ‘water cooler effect’ where employees simply warn each other, which invalidates the test results. This gives security teams
Can these tools simulate deepfakes?
Leading tools are beginning to incorporate “vishing” (voice phishing) and deepfake elements. Hunto and Proofpoint are at the forefront of multimodel threat simulation, preparing users for attacks that happen outside the inbox.
What is the best metric to track?
Stop tracking “Click Rate” alone. It is a vanity metric. Focus on Reporting Rate (how many people reported the phish) and Mean Time to Report. A low click rate means nothing if no one tells the SOC that an attack is in progress.
How do I get started with Hunto’s phishing simulation agent?
You can deploy Hunto’s phishing simulation agent in minutes. It integrates with Google Workspace and Microsoft 365 to start mapping your human risk profile immediately. Check out our Customers page to see how other organisations are automating their human defence.
Conclusion
The goal of phishing simulation is not to trick employees; it is to build a reflexive muscle memory for threat detection. In 2026, that requires tools that are as dynamic and intelligent as the threats themselves. Whether you choose the massive library of KnowBe4, the gamification of Hoxhunt, or the autonomous precision of Hunto.ai, the key is to start now.
The adversary is automated. Your defence must be too.
